Guidance for handling a ransomware attack
Posted on 8th April 2022 at 09:30
With high profile data breaches and ransomware attacks seemingly ever-present in our news feeds, we need to accept that it is more likely when than if it happens to you.
It is not only important to understand how to respond to cyber-attacks, but also how to respond quickly, and with the most effective solution, which often isn’t paying a ransom demand, and how to recovery from ransomware attacks.
Recovery from ransomware attacks
What are the latest ransomware trends?
A recent article by Tech Digest stated that 91% of enterprises have been hit by ransomware, and that only 11% of executives felt confident that they could recover in two days or less. Further, the downtime costs (for companies with over 10,000 employees) were estimated to be in excess of $10m per day.
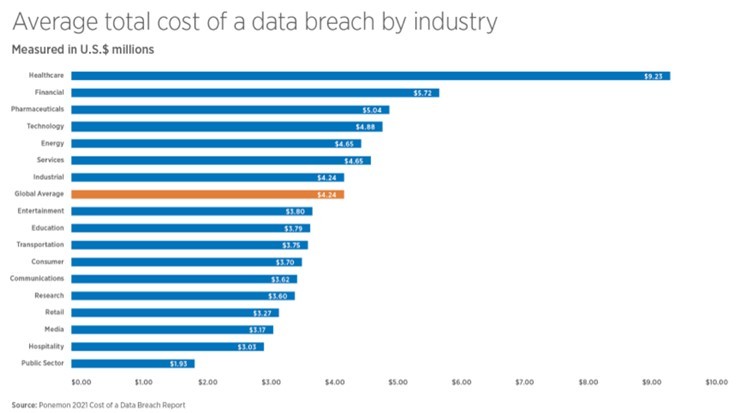
But whilst the more highly regulated industries seemingly suffer the hardest financially, ransomware attacks afflict a much wider group.
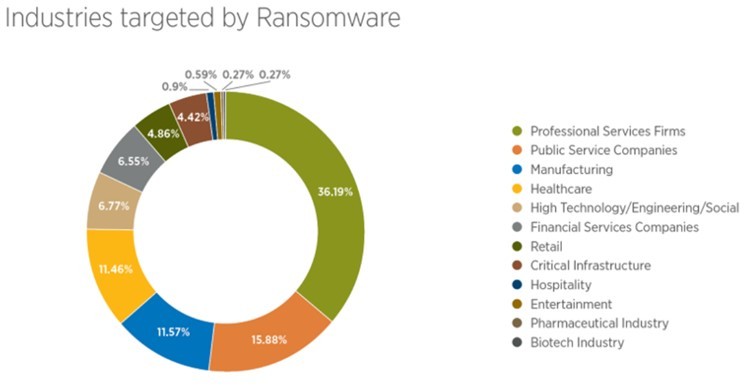
If we look at the volume of attacks by industry, we see that 36% fall on professional services firms and 16% on public service companies.
The next most-targeted segments are manufacturing and healthcare, but really, no industry (or individual for that matter) is safe from the attentions of bad actors and cyber-crime.
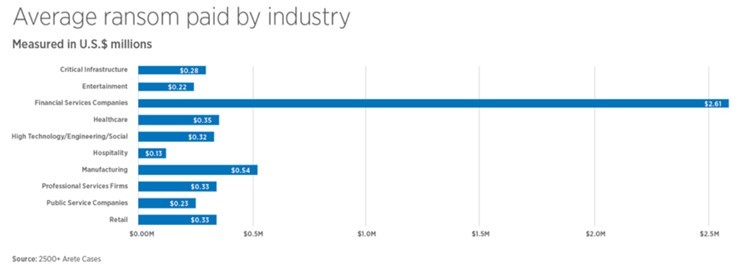
In terms of what the actual ransom cost itself looks like, again the financial services companies bear the brunt with average ransom payments reaching an astronomical $2.61m.
The ransom demands are far from arbitrary, often being determined by the perception of how able the company is to pay, and also the value of the data stolen, be that operational, financial or reputational cost.
So with the increase in both the volume and cost of cyber incidents, it is important to understand the variables to consider when responding to an attack.
Should I pay the ransom?
It can be very tempting to bite the bullet and pay up to avert further reputational or financial damage, or even to try and sweep the whole incident under the carpet. But there are several reasons why this might not be the best place to start.
1) There is a high chance that your data will not be fully decrypted, with larger file types particularly prone to being returned in a corrupted state, and frequently unusable as a result. A recent report by Help Net Security suggested that as little as 14% of companies were able to get back all of their data after paying the ransom.
2) By paying the ransom you are sending a very strong signal about both the value of your data and your ability and willingness to pay for it. This opens up a very real risk of further or more sophisticated attacks such as double extortion (your data is exfiltrated for leverage) or triple extortion (the exfiltrated data is accessed to contact data owners or customers to apply further pressure).
3) You are funding criminal behaviour, which only serves to perpetuate this detestable industry costing businesses and taxpayers alike billions annually. Furthermore, in some countries you might actually be committing an offence yourself by paying the ransom, for example if the threat actor is OFAC-sanctioned.
Conclusion: It is not advised to pay the ransom as a first step, there are usually other options to explore before it comes to that.
Can my insurance company help?
Some companies have specific cyber cover, some have a measure of cover included in more standard policies, others are not covered at all. You need to find out straight away.
1. It is therefore certainly imperative to put a call into your insurance provider without delay, if for no other reason than to check your level of cover, understand what excesses might be in play, and establish what impact a claim might have on future policy renewals. All of this is important when gauging the most financially viable solution to your situation.
2. In addition to potentially paying for the resolution of your cyber-attack, your insurer will also be able to offer sound advice and potentially resources to help mitigate the impact. After all, they will have helped customers navigate these situations thousands of times before, and it is in their interests too to get your problem resolved quickly and cost-effectively.
3. Specifically, your insurer will also likely have a team of ransom negotiators on staff, with experience to significantly reduce the payout and also facilitate the payment itself. (For example, not many individuals have $1m+ of Bitcoin readily available.) They will also know the best strategy for negotiation which can help maximise the quality of the decryption and minimise the delay.
Conclusion: Your insurance company can be a key ally after a cyber event, and it is highly recommended to engage them in the early stages.
Are there data recovery alternatives?
Professional data recovery companies that have capabilities to recover data after a ransomware attack are few and far between, but there are a handful of excellent ones that offer a credible alternative to paying a ransom.
They will be able to deploy custom decryption, undelete, walk back and rebuild tools to resolve the problem in many cases, or review how far and wide the attack has spread to see if a recent alternative version or backup of the data exists.
Solutions will exist for single devices, virtual and RAID servers, even backup tapes and other media.
1. Engaging a data recovery expert is usually cheaper than paying a ransom, and most certainly a more ethical and security-conscious solution that funding the cyber-criminals. In most cases, an initial evaluation of recovery options is free, or charged at a nominal cost, and can be undertaken quickly.
2. Often, recovered data will be more complete / usable than data which has been decrypted by the threat actor, thus saving cost replicating missing data or repairing files that have been damaged in the process.
3. By not engaging with the cyber-criminal, and showing that you have resilience to their attacks by recovering your data a different way, you send a strong message that you will not be blackmailed and therefore there is little value to them in pursuing you further. Hopefully that will reduce the risk of future attempts to extort money from you.
Conclusion: there is every chance that a professional data recovery expert will be able to offer you a cheaper, better, safer and (importantly) legal alternative to paying a ransom, but you need to make sure you select a provider with the requisite skills and experience.
What peripheral implications should I consider?
Dealing with the immediate pressures and impacts of having your systems compromised and your data restricted is of course of the utmost importance, and should be a priority as the costs associated with downtime are huge. But that isn’t the end of the story.
1. You should employ a forensic investigator to help you understand how the attack occurred, how far and wide the damage spread, what traces if any remain, and of course how to prevent an attack from occurring again in the future. Forensic investigators are routinely available through competent data recovery companies, some insurers, or independently.
2. It is also imperative, of course, to limit the reputational harm a cyber breach can cause, which is sometimes the most costly impact. Expert breach coaching and cyber incident response services will help frame the containment, support customers and staff through the incident, and communicate clearly what measures have been put in place to prevent a repeat, which will allay fears and reduce reputational damage.
3. The steps taken after a ransomware attack are not only imperative to prevent further attacks and shore up confidence in your business, but they also have a significant impact on your future insurance premiums, terms of insurance, and sometimes can even determine whether you will even be offered insurance at all!
Conclusion: there are steps to take after a cyber event not only to protect your data going forward, but also to ensure that your business is seen as safe and viable by all stakeholders and suppliers, and attacks should always be viewed in this wider context.
Steps to take after recovery from ransomware attack
In summary, there is a lot more to successfully navigating a cyber-attack than simply paying the ransom and hoping for the best. That is assuming, of course, that you even have the ability to pay the ransom in the first place. Thankfully, help is at hand.
1. Do not pay the ransom straight away. Disconnect your infected devices from the network, do not attempt to run any tools, do not attempt to restore from backups. If possible, do not engage with the threat actor at all just yet, leave that to the professionals.
2. Call your insurance company. They need to know, and will be able to advise not only on your level of cover, but will have teams of cyber response specialists and negotiators available to assist you. It is in your mutual interests to resolve this quickly and effectively.
3. Contact a data recovery expert to review alternative ways to recover your data. This will likely be cheaper and more secure than paying a ransom, and hopefully reduce the likelihood of you being targeted again in the future. They also have forensic investigators on staff to help understand how the breach occurred, and how to prevent it from happening again.
4. Engage a breach response team to manage the reputational impact and ensure that the stakeholders in your business are getting transparent and timely information about the situation directly from yourself, rather than from the media or the cyber-attacker.
5. Get certified for Cyber Essentials Plus, perform a full review of your system security and engage a penetration testing firm to check your defences. Train your staff about cyber risk. Train your staff again. This sends the right message to your customers, reduces future insurance premiums, and helps prevent the often devastating impacts of cyber crime in the future.
Conclusion: cyber-attacks are very challenging and emotional for your business and customers, but there are many companies that can help you navigate successfully. Don't try and work this out on your own, and don't delay - reach out for help as soon as you suspect a breach.
Need help with recovery from ransomware attack?
Share this post: